
Innovating IT Management with Changed Admin Access Flows

Innovating IT Management with Changed Admin Access Flows
If you’ve ever tried running a program on Windows as an administrator, you’ve probably come across a prompt asking you to either give or deny it permission to make high-level changes. That’s User Access Control (UAC) in action, and it adds an extra layer of security when a program or task is seeking elevated privileges. This gives you the chance to stop unwanted or malicious software from making changes on your PC.
As an administrator, you can change how UAC behaves. In this guide, we’re going to show you how to do that using the Local Group Policy Editor and Registry Editor.
What Behaviors Does UAC Have for Administrators?
Before you go about changing the way UAC acts for administrators, it helps to know what behaviors you can choose and what they mean. We’re going to list them below, along with the definitions that are listed on Microsoft Learn .
Here’s what you can choose:
- Elevate without prompting: Assumes that the administrator will permit an operation that requires elevation, and more consent or credentials aren’t required. This minimizes the protection that is provided by UAC.
- Prompt for credentials on the secure desktop: When an operation requires elevation of privilege, the user is prompted on the secure desktop to enter a privileged username and password. If the user enters valid credentials, the operation continues with the user’s highest available privilege.
- Prompt for consent on the secure desktop: When an operation requires elevation of privilege, the user is prompted on the secure desktop to select Permit or Deny. If the user selects Permit, the operation continues with the user’s highest available privilege.
- Prompt for credentials: An operation that requires elevation of privilege prompts the administrator to type the username and password. If the administrator enters valid credentials, the operation continues with the applicable privilege.
- Prompt for consent: An operation that requires elevation of privilege prompts the administrator to select Permit or Deny. If the administrator selects Permit, the operation continues with the administrator’s highest available privilege.
- Prompt for consent for non-Windows binaries: This prompt for consent is the default. When an operation for a non-Microsoft application requires elevation of privilege, the user is prompted on the secure desktop to select Permit or Deny. If the user selects Permit, the operation continues with the user’s highest available privilege.
Now that you’re familiar with the UAC behaviors for administrators, let’s see how to change them.
Changing UAC Behavior for Administrators in the Local Group Policy Editor
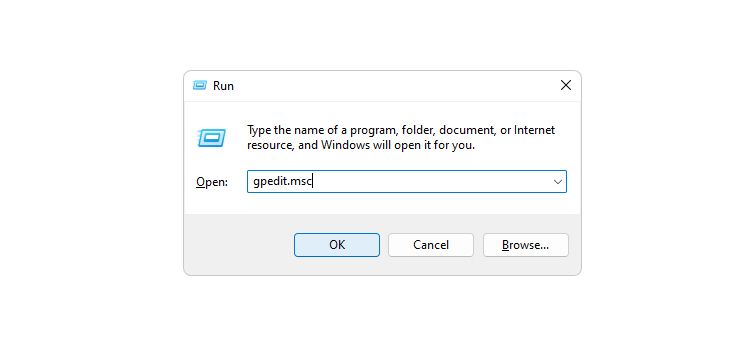
To change the UAC behavior for admins using the Local Group Policy Editor (LGPE), start by pressing Win + R, typing gpedit.msc in Windows Run, and hitting the Enter key to open the LGPE on Windows .
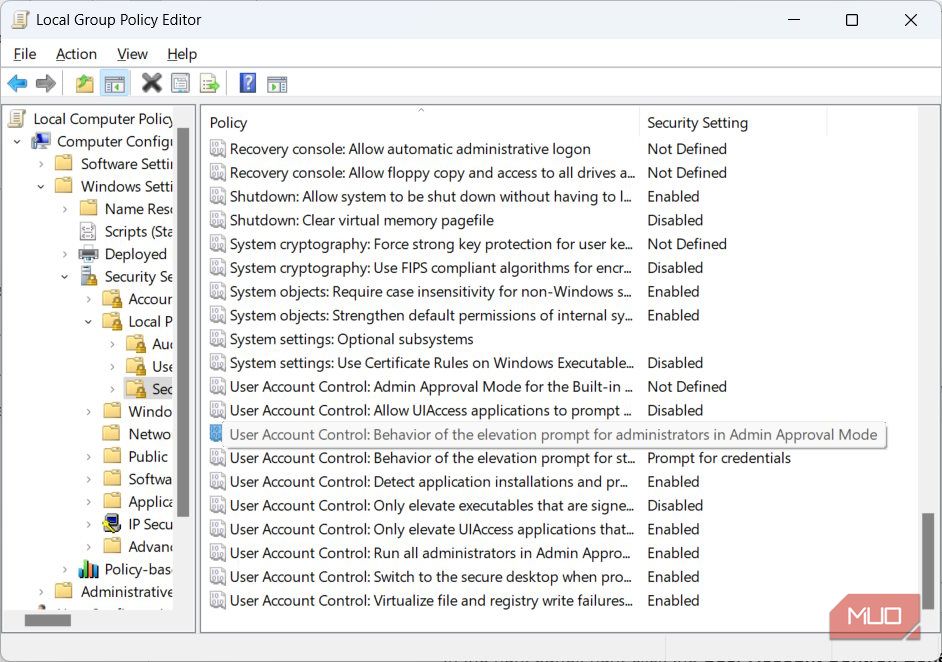
In the left panel, navigate to Configuration > Windows Settings > Security Settings > Local Policies > Security Options. In the right panel, double-click the User Account Control: Behavior of the elevation prompt for administrators in Admin Approval Mode policy to access its Properties window.
Click on the dropdown and select the UAC behavior you want.
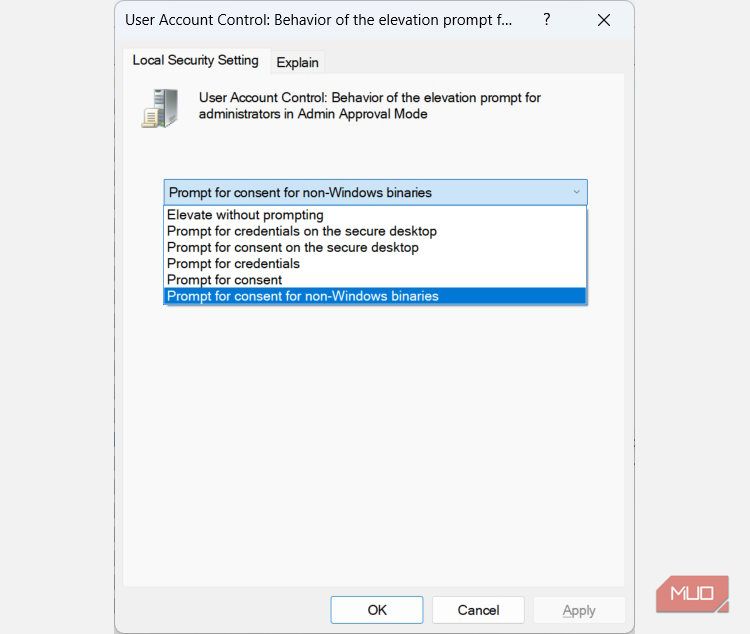
To apply and save the changes, click on OK.
Changing UAC Behavior for Administrators in the Registry Editor
To change the UAC behavior for administrators using the Registry Editor, start by pressing Win + R, typing regedit in Windows Run, and hitting the Enter key.
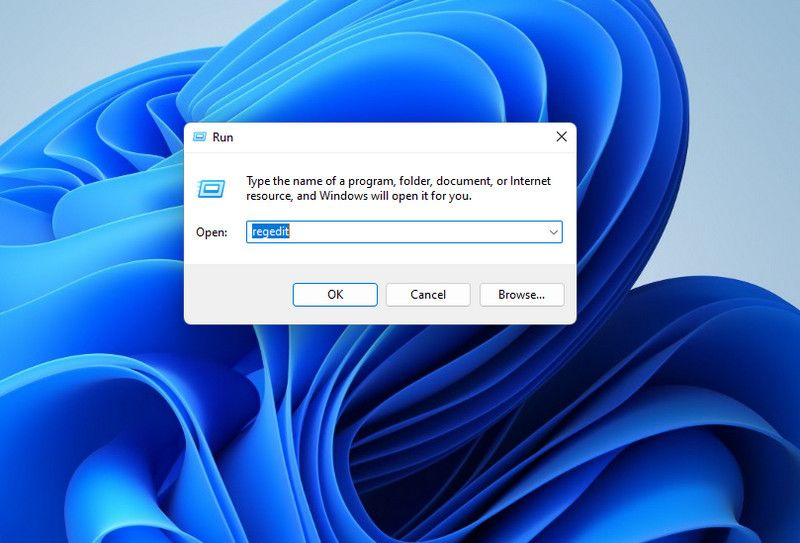
In the UAC prompt, click Yes to open the Registry Editor on Windows .
Changing settings in the Registry Editor can impact the performance of your computer negatively if you make a mistake. To make sure you always have a way to revert the changes, we recommend learning how to back up and restore the Windows Registry .
In the navigation panel on the left, head to HKEY_LOCAL_MACHINE > SOFTWARE > Microsoft > Windows > CurrentVersion > Policies > System. In the right panel, double-click the ConsentPromptBehaviorAdmin value to modify it.
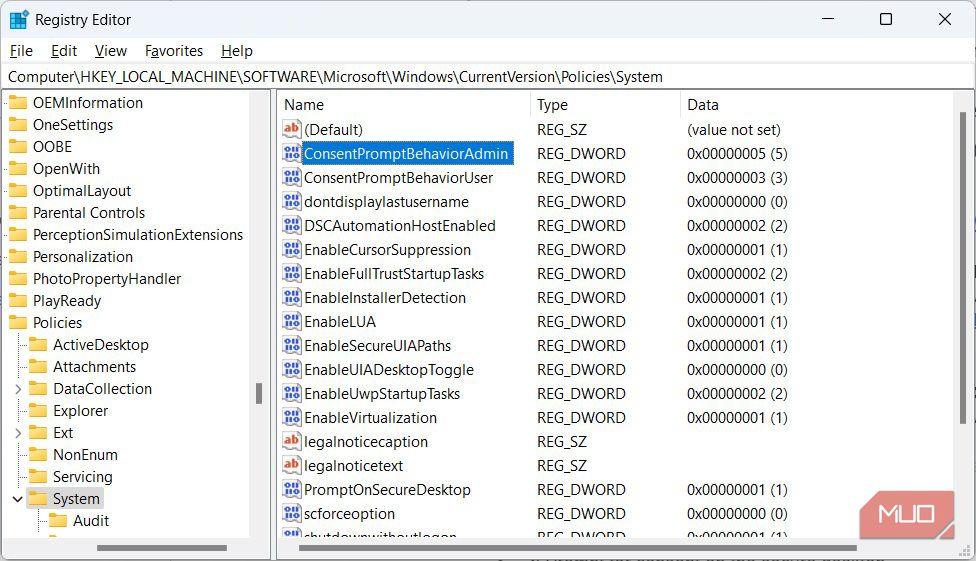
Enter one of the following variables in the text box for Value date:
| Variable | UAC Behavior |
|---|---|
| 0 | Elevate without prompting |
| 1 | Prompt for credentials on the secure desktop |
| 2 | Prompt for consent on the secure desktop |
| 3 | Prompt for credentials |
| 4 | Prompt for consent |
| 5 | Prompt for consent for non-Windows binaries |
So, if you were to, for example, change it to Prompt for credentials, you’d enter 3 in the Value data text box.
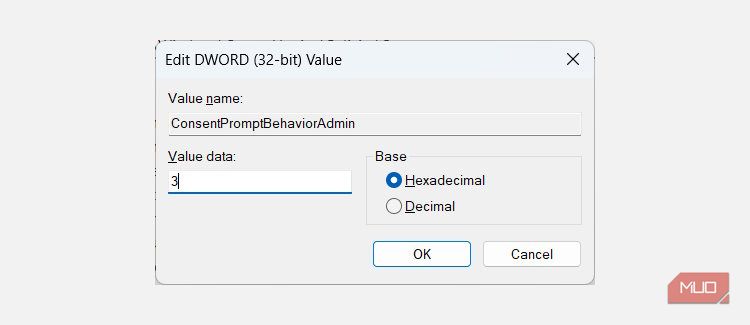
Then, click OK to apply and save the changes.
Control the UAC’s Behavior as an Administrator
Now you can change the behavior of UAC for admins as you please, depending on your situation. Just be careful not to make your computer more vulnerable in the process, which can happen if you choose Elevate without prompting. Microsoft recommends using that option only when you’re in a highly secure environment where the administrator accounts are tightly controlled.
In that case, you can even disable the UAC altogether if you’d like since you know there are other measures in place to protect your computer from unwanted or malicious programs.
As an administrator, you can change how UAC behaves. In this guide, we’re going to show you how to do that using the Local Group Policy Editor and Registry Editor.
Also read:
- [New] Mellow Moves Discover Top 20 Serene Country Songs for Groovy Dancing (TikTok)
- [Updated] Ultimate Guide to Non-Udemy Online Education Sites for 2024
- 2024 Approved Excellent Choices Comprehensive Paid & FREE Mac/PC Video Decoders
- Adding Various Keyboards on Gmail's Web Interface: A Comprehensive Guide
- Diving Deep Into Drive Space Analysis Using Windows DiskUsage Command
- Essential Picks for Every Academic's Toolkit: The Ultimate Guide to College Laptops Tested and Reviewed | ZDNET
- Expert Advice on Successfully Updating Your Audio Technica Sound Card Drivers
- Improving Chrome’s File Saving Mechanism on Your Windows Computer
- In 2024, Life360 Circle Everything You Need to Know On Tecno Pop 7 Pro | Dr.fone
- Mastering Charge Alerts for Windows Devices
- Maximizing Mouse Control in Windows 11: Accessibility Guide
- Navigating Through the Complexity of Security Faults
- Title: Innovating IT Management with Changed Admin Access Flows
- Author: David
- Created at : 2024-12-05 17:54:47
- Updated at : 2024-12-07 03:06:37
- Link: https://win11.techidaily.com/innovating-it-management-with-changed-admin-access-flows/
- License: This work is licensed under CC BY-NC-SA 4.0.